By Matthias Kohlbrand In
Our service includes setting up variuos user groups with specific permissions during installation of a software system for a client. Through a jointly established user concept, this assignment of permissions can be optimised to correspond exactly to your wishes. First of all, the assignment of the relevant software modules determines which functional operations are available in principle to an individual user once they login to the Cosmino software. Active directory and LDAP can of course be supported.
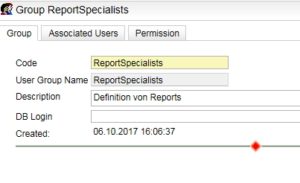
For each software module, there are predefined user groups (e.g. operator, admin, etc.) for which various permissions are conveniently preconfigured. All that needs to be done is to assign the users to the right group for the permissions they need (n:m relationship).
Here, expansion of the predefined groups and permissions is possible. Because each entry in the menu structure can be hidden. In the screens themselves, it is even possible to differentiate between read and write access.
Since the beginning of this year, access to specific data can also be restricted for users and user groups. All data, collected or created, is associated with hierarchically stored master data. This makes it possible to configure the system such that users only have access to data for specific hierarchy levels, machines, people, groups of people, tools, cost centres. Depending on what level of the master data hierarchy a restriction is set up at, access is only available accordingly to the lowest level, so to individual machines, tools, cost centres and people, or at a higher level for everything which is below that level in the hierarchy.
Whether access to the defined data is prevented or explicitly only allowed here for users can be configured. As a result, it is even possible to give Mr Mustermann access to all machine groups with the exception of groups 3 and 6, for example. In group 3 which he can’t see, however, he has the permissions to access the data for machines 3, 4 and 7.
This restriction pertains to both the master data in this area and to the raw data collected and its validated counterpart.
The restriction of permissions and access for users protects sensitive data on one hand and the software configurations and master data on the other. This is just as important for the operation of production-related software as data archiving and protection against malfunctions.
 This restriction pertains to both the master data in this area and to the raw data collected and its validated counterpart.
The restriction of permissions and access for users protects sensitive data on one hand and the software configurations and master data on the other. This is just as important for the operation of production-related software as data archiving and protection against malfunctions.
This restriction pertains to both the master data in this area and to the raw data collected and its validated counterpart.
The restriction of permissions and access for users protects sensitive data on one hand and the software configurations and master data on the other. This is just as important for the operation of production-related software as data archiving and protection against malfunctions. 
